Article
Extending Zero-Trust Security
to Industrial Operations

By Insight Editor / 24 May 2022

By Insight Editor / 24 May 2022
Recent cyber attacks on industrial organizations and critical infrastructures have made it clear: operational and IT networks are intimately linked. With digitization, data needs to seamlessly flow between enterprise IT and industrial OT networks for the business to function. This tighter integration between IT, OT, and Cloud domains has increased the attack surface of both the industrial and the enterprise networks.
The traditional security perimeter that industrial organizations have built over the years by installing industrial demilitarized zone (IDMZ) is no longer sufficient. While this is still the mandatory first step to protect operations, embracing the digital industry revolution requires additional security measures, assuming that no user, application, or connected device can always stay trustworthy.
The Zero Trust Security model that many are now implementing to secure the enterprise workforce, workloads, and the workplace must be extended to industrial operations. It establishes an initial level of trust for all connecting entities based on their business role, enforces it through the network infrastructure, and continuously verifies this level of trust and compliance in every access request. It identifies not just users, but endpoints, and applications to grant them the absolute minimum access they need.
Being the leader in both the cybersecurity and industrial networking markets, Cisco is probably the only vendor on the market offering a comprehensive, validated architecture for extending Zero Trust Security to industrial workplaces.
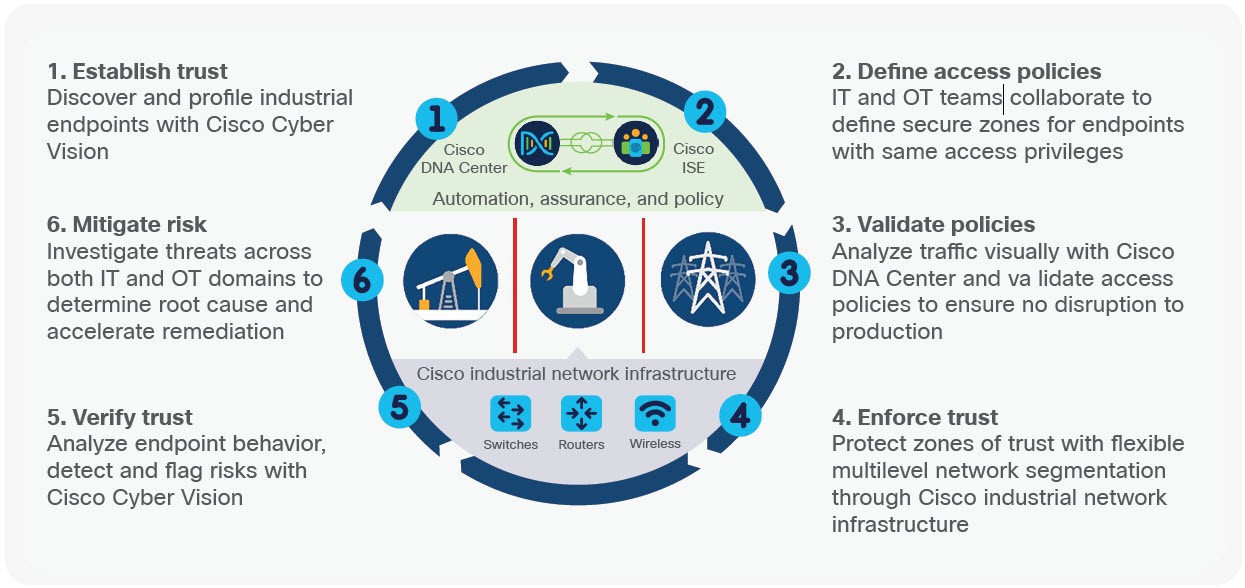
Cisco Cyber Vision is designed to help industrial organizations gain visibility into their industrial network, discover all devices, identify known vulnerabilities, determine risks, and detect threats or abnormal behaviors. Because it is built into Cisco industrial network infrastructure, Cyber Vision can be deployed at scale without the need of additional appliances or out-of-band collection network.
This detailed list of industrial devices is shared in real-time with Cisco Identity Services Engine (ISE) where security policies are created. Once IT and OT have defined the industrial zones or production cells they want to secure, IT will create Security Group Tags (SGT) in ISE to specify which communications are allowed between zones. OT users now just have to place industrial devices into the corresponding group using the Cyber Vision graphical interface for the right security policy to be automatically applied to them.
Downtime is very disruptive in industrial environments, so it is vital to monitor policy behavior before enforcement. The Policy Analytics module in the Cisco DNA Center network management platform lets you visualize real time traffic flows between groups to ensure your policy will not block communications that are required for the industrial process. Once you are confident with the monitored policy, you can activate the policy enforcement through Cisco DNA Center.
This simple workflow enables effective collaboration between IT and OT to define zone segmentation and enforce Zero Trust in the IoT/OT network. IT leverages tools designed to manage and secure networks. OT remains self-sufficient by using a tool that understands the industrial process. New devices will not be allowed into the network until OT places them in the production zone they belong to via a simple drag and drop within Cyber Vision. Moving a device from a zone to another will automatically modify the security policy applied to it.
Zero Trust doesn’t stop once access has been granted. Communications from and to industrial devices must be monitored to identify malicious traffic and abnormal behaviors that could disrupt production. As Cyber Vision is embedded into the industrial network, it sees everything and continuously decodes application flows to detect threats by leveraging signatures from Cisco Talos and behavioral baselines defined by OT. All these security events are reported to Cisco SecureX for investigation and remediation.