The main problem with the devices exploited in the attack was that they lacked robust security features.
Easily-guessed usernames and passwords were compromised, allowing the hacker to take control of millions of internet-connected devices for their own purposes. It’s not clear whether it resulted in a data breach or the hacker(s) were simply flexing their muscles to test vulnerabilities. Regardless, the cost of disrupted business continuity is always far-reaching.
What is endpoint security?
Endpoint definition: an endpoint is basically an internet connected piece of hardware like a laptop, computer, tablet, printer, smartphone, thin client, or even a POS system. With the scope of ever-expanding smart devices in modern workplaces and homes, almost anything can be an endpoint. These connected devices can allow unauthorized access into your vital data when they are not properly secured.
Endpoint security means making sure these devices comply with company policies before they are granted network access, to prevent a costly and dangerous security breach. Endpoint protection includes more than just antivirus software. Endpoint security software starts with the main client, is distributed to devices and is then usually managed from a command post within an enterprise or midsize company. A company’s central server hosts the software and regulates what devices can connect to the network based on log-ins, detected file types and more.
Antivirus software is hosted on a computer and eliminates detected viruses from that particular device for data breach or malware protection. Keeping updated antivirus software on a computer will keep the virus from spreading once that device is connected to the internet. Antivirus software is typically one component of the larger endpoint security software suite that a company should run.
An easily overlooked endpoint: Printers
In the past, most companies felt that their environment was secure if they had a high firewall established. They trusted that all the devices inside it were OK. Now, security teams are realizing that everything that touches their network needs to either be secure or have a security policy established with it. Company networks are vulnerable environments — just consider how many phishing emails get into employee inboxes and launch malware.
Conversations with IT professionals regarding printer security are changing. Security teams are now driving more conversations around printing and are also involving corporate C-suite executives. As a result of rising security breaches, senior executives are more willing to invest everywhere necessary to ensure their environments are protected.
A 2015 Ponemon Institute report stated that 64% of IT managers believe their printers were infected with malware, and that 56% of enterprises ignored their printers in their endpoint security strategy. With that in mind, companies like HP are building printers that include security measures. New features such as detection and “self-healing” recovery from attacks, whitelisting of known and accepted firmware, and Run-time Intrusion Detection, which provides in-device memory monitoring for attacks, are now standard features on HP LaserJet Enterprise and OfficeJet Enterprise X printers with HP PageWide Technology. HP also offers a policy-based printer security compliance solution called JetAdvantage Security Manager, to help create an entire security system around its printers.
How do you get reliable endpoint security?
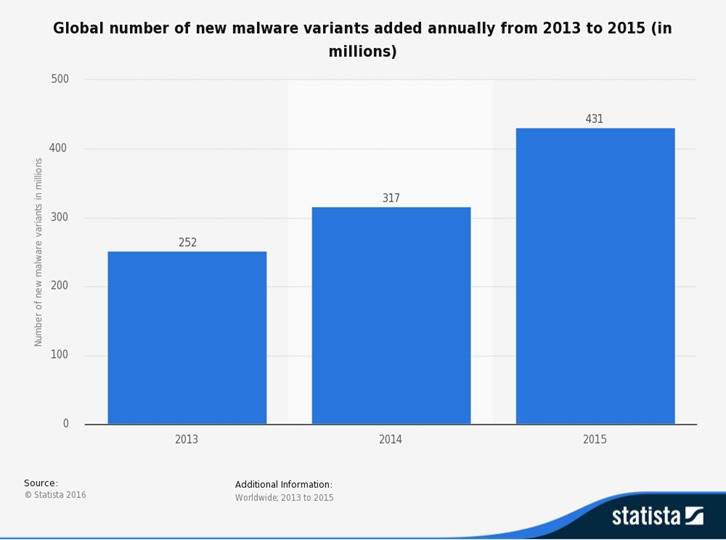
The threat landscape is escalating rapidly in both numbers and complexity. Today, targeted attacks and zero-day vulnerabilities are the two most common advanced threats. A zero-day vulnerability could result in more attacks, since anyone could easily leverage a malware toolkit that’s readily available on the internet. Moreover, zero-day vulnerabilities are discovered only after they are exploited by attackers.