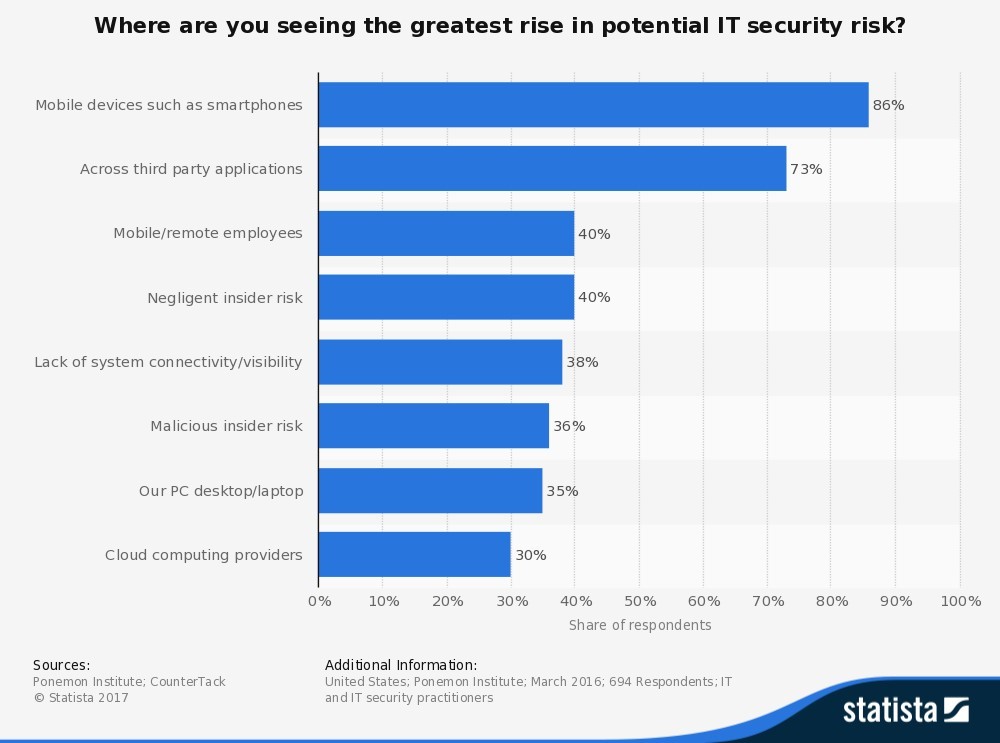
Figure 1 identifies areas where the IT security respondents saw the greatest rise in potential IT security risks: 86% said mobile devices, 73% said third-party applications, 40% said mobile and remote employees, 38% said negligent insider risk, 36% said lack of system connectivity or visibility, 35% said their PC desktops and laptops, and 30% said cloud computing providers.
In spite of the risks associated with endpoint devices, companies need BYOD policies to stay competitive in today’s growing market.
In order to give your team the fast, reliable and flexible work environment they need to help your business grow, mobility is a must. With the right controls and management practices integrated into your small business security strategy, you can leverage BYOD to increase efficiency, reduce company device costs, and create better employee and customer experiences.
Creating a mobile device management and BYOD security solution
The first step in developing a proper mobile strategy is to evaluate your current state of business. Ask yourself the following questions:
- Which teammates deal with critical, sensitive data?
- What devices will be permitted for work use?
- What software solution will you need to secure cloud application access?
- What additional tools can you set up for backup and recovery?
- What restrictions need to be put in place?
Forrester has created a risk continuum to guide BYOD security decision-making. It suggests that employees who fall into the low-risk profile and need basic applications to complete everyday assignments can jump in with open access and little or no security, controls or restrictions. Those who have a high-risk profile and deal with critical company data, customer information and employee credentials need to be restricted to corporate devices. Those in between are eligible to access personal devices with security controls in place to make sure applications, browsers and documents are secure.
It’s important to note that successful BYOD security policies must be adaptable since they fluctuate according to changing teammate job functions, work requirements and technology. According to the Forrester report, when businesses look for tools to better manage security around devices, many companies:
- Use containers to separate corporate and personal apps and content.
- Secure productivity apps for content and notes.
- Secure browsers for cloud and corporate data access.
- Customize network access controls for secure connectivity.
Mobility isn’t slowing down — neither should you.
The hit single “9 to 5” was released in 1980, when workers were tethered to their desks. Today, smartphones and laptops are basic accessories, enabling employees to complete their tasks whenever and wherever they choose.
Don’t let security concerns deter you from enabling greater flexibility and mobility for your business. Start by addressing your core business needs and develop a BYOD program that fits your objectives. Once you have a solid practice in place, continue to provide training and support to help your teammates manage and use their devices effectively.
As a result, your business will save money, increase productivity and boosts employee satisfaction.