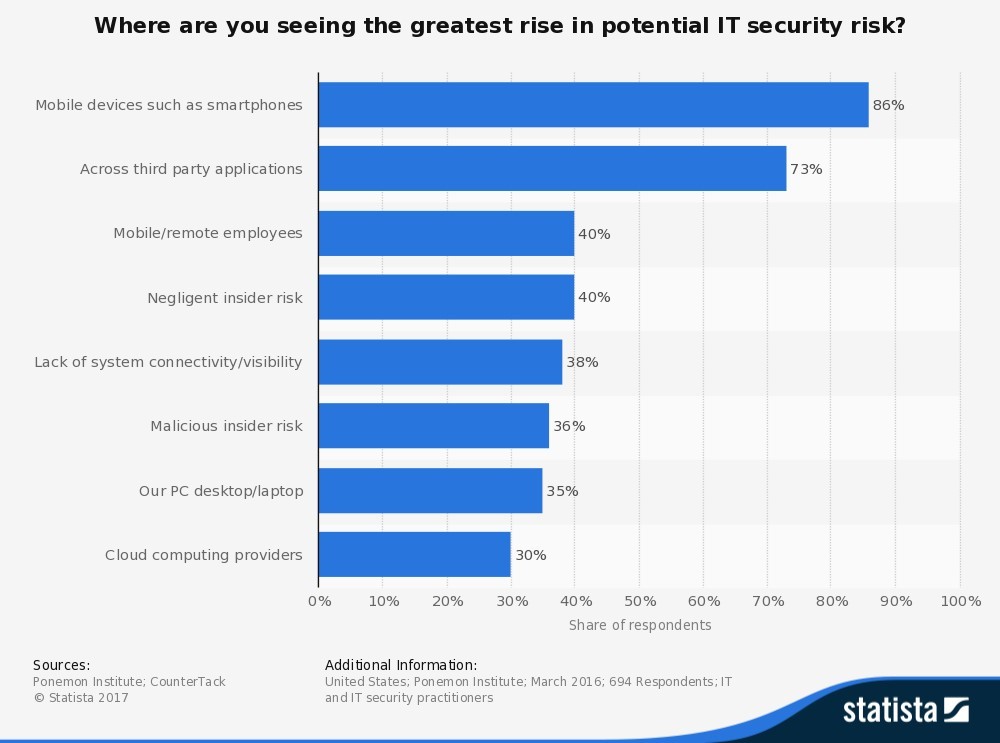
Figure 1 identifies areas where the respondents saw the greatest rise in potential IT security risks: 86% said mobile devices, 73% said third party applications, 40% said mobile and remote employees, 38% said negligent insider risk, 36% said lack of system connectivity or visibility, 35% said their PC desktops and laptops, and 30% said cloud computing providers.
How can you avoid costly security breaches and data risks across multiple devices that are connected to the cloud? Microsoft Enterprise Mobility + Security (EMS), formerly known as the Enterprise Mobility Suite, uses identity-driven security solutions that are designed to provide secure access to the apps and resources your employees need — and detect threats before they arise.
Microsoft EMS protects corporate information by limiting the usability of the data within a managed environment and embedding access controls directly into encrypted files. EMS also automatically enrolls devices, then enforces policies that allow users to access applications.
Simple and secure identity management solutions
Identity management, device management and information protection were once done entirely within an organization’s on-premise environment. This required manual configuration of point-to-point connections between organizations. Today, enterprise computing includes Software as a Service (SaaS) applications, cloud platforms and more.
When data is more valuable than dollars, your business needs a holistic, hybrid approach to centrally manage identities across the organization. Two Microsoft EMS solutions that help IT protect access to applications and resources include Azure Active Directory and Multi-Factor Authentication.
Azure Active Directory (Azure AD) is Microsoft’s multi-tenant cloud-based directory and identity management service that enables Single Sign-On (SSO) access to SaaS applications like Office 365, Salesforce, DropBox and Concur. Azure AD SSO works across all devices to ensure employees are able to access the resources they need to work effectively.
SSO ensures that users go through an authentication process to prove that they are who they say they are. With monitoring, reporting and self-service IT, Azure AD is a hybrid solution for on-premise and cloud application access. This way, employees who are frequently on the move and beyond the company firewall, can still work in confidence.
What is authentication? Azure Multi-Factor Authentication is a two-step identity verification system that requires two or more of the following methods:
- Something you know (Password)
- Something you have (A trusted device)
- Something you are (Biometric screening)
Windows Azure Multi-Factor Authentication is quick and easy to setup, use and scale when connected to on-premise or cloud applications. Whether employees choose to receive a phone call, text message, mobile app notification or verification code, they can rest assured that their sensitive data is secure.
Empower employees and protect your business
You can keep your employees productive and protected with identity-driven security as part of your mobile strategy. Microsoft EMS is designed to simplify the process of delivering a complete identity and device management solution that meets end-user needs for secure SaaS application access from multiple devices.